Verified Mirrors
Each mirror address is checked against the current PGP announcement. Rotation happens every 7 to 14 days based on load patterns and phishing activity. We republish only addresses signed by the original Vortex key.

./connect --verified --brand=vortex --tor-only
An informational guide for locating verified Vortex mirrors in 2026. Check current uptime status, confirm PGP signatures, and follow basic opsec before connecting.
Three onion addresses, all cryptographically signed with the same PGP key that has been in use since Vortex launched. Any mirror routes to the same backend — pick whichever responds fastest from your circuit.
Loading...
Loading...
Loading...
Vortex is a Tor-based marketplace operating since mid-2024, serving 84,969 registered users across its current infrastructure. The platform runs on a set of rotating onion mirrors with 96.5% measured uptime over the past 90 days. Unlike newer entrants, Vortex uses a vendor-level escrow system with mandatory PGP authentication for account actions. This page exists as a reference point: we track confirmed mirror addresses, signature verification procedures, and known clone attempts. Nothing here is a recommendation to transact; it is practical information for users who already run Tor and understand the risks involved.
The marketplace lists 13,375 active products from 2,111 vendors in its current inventory snapshot. Categories range from digital goods to physical items, each with vendor-specific review histories visible on the market itself. Vortex staff publish signed announcements on known forums including Tor Project community channels, Dread, and a handful of mirror directories, which helps filter out phishing copies. The original PGP key has remained consistent since launch, which is the single most reliable indicator of authenticity when you encounter a new mirror address claiming to be official. Never trust an address posted without a matching signature.
We update this page when Vortex staff rotate to a new primary onion address or when a clone campaign gains traction in search results. The clearnet domain you are on now is a directory, not the marketplace itself. Any transaction attempt here would be a scam. The actual market lives on Tor and requires the Tor Browser to reach. If a page ever requests your market credentials outside of the .onion address listed below, close the tab. That pattern is the most common entry point for credential theft in 2026. See Privacy International and Amnesty Tech for broader context on digital rights and surveillance risk.
A note on what this directory is not. We do not run Vortex, we do not take a cut of transactions, we do not broker disputes, we do not hold funds in escrow, and we do not receive referral credit from the market. The relationship is purely informational: we publish addresses that pass our verification checks and we remove addresses that do not. If that sounds thin, it is meant to. Tor directories that claim to be more than this — offering "premium access," "verified vendor lists," "faster mirrors" — are almost uniformly scams. An editorial directory is the right model. Anything beyond that introduces incentives that work against users. Readers who want a deeper background on the economics of Tor marketplaces can start with publicly archived research on Internet Archive, which preserves years of community analysis on how these platforms evolve under enforcement pressure.

Four reasons this page stays current while many older clone directories drift out of sync. Each check runs independently — we do not rely on staff announcements alone.
Each mirror address is checked against the current PGP announcement. Rotation happens every 7 to 14 days based on load patterns and phishing activity. We republish only addresses signed by the original Vortex key.

Account creation and all sensitive actions require PGP. No phone numbers, no email verification, no KYC requirements of any kind. The market rejects plaintext login attempts by design.

Measured across the past 90 days using independent probes running every 15 minutes. Short outages are documented in the community changelog within hours of detection. The data is not staff-reported.
84,969 registered accounts and a moderated subdread for dispute discussion. Vendors respond in the open channel when issues come up. Transparency is measurable through public thread activity.

Every address on this page went through three independent checks before publication. We do not take staff announcements at face value. Phishing campaigns have learned to imitate staff posts convincingly in 2026, so signature work is the only reliable defense.
The onion address must appear in a clearsigned announcement from the original Vortex PGP key. We hold the key fingerprint temporarily inaccessible on paper. Every new mirror we receive gets checked against the temporarily inaccessible copy first. If the fingerprint drifts by a single character, the mirror does not get published. This has already filtered out two clone campaigns this year, both of which used newly generated keys with similar human-readable names.
A valid mirror appears in at least two independent channels signed by the same key. Dread, the official forum thread, and a handful of aggregators each carry the signed post. A mirror that only appears in one place triggers a longer waiting period and additional checks. Users on Matrix discussion rooms frequently spot clones first, and we incorporate their reports when a mirror shows inconsistent fingerprints across channels.
Each published mirror gets polled every 15 minutes from three different Tor circuits. A consistent response, consistent TLS fingerprint if applicable, and matching homepage hash across all circuits confirm the mirror is routing to the real backend. Any divergence pulls the mirror from this page within the next probe cycle until the issue resolves. The probe log for the past 90 days is what produces the 96.5% uptime figure cited above.
If you land on a page that claims to be Vortex and any of the following are true, close the tab. Confirmed phishing sites reuse these patterns.
"The simplest rule: addresses do not come from search results, they come from signatures. Search is how phishing finds you."
— operator commentary, Dread /d/OpSec thread, April 2026
Eight steps for a clean first connection in 2026. Move through them in order. Skipping the PGP setup before depositing is the most common reason new users lose funds — do not do that.
Get Tor Browser only from torproject.org. Any other source risks a tampered build that can log your traffic and break anonymity. Verify the download signature using the public key published by the Tor Project. On Linux, a separate option is Kali or Tails, both of which ship pre-hardened. Need a quick check? Open the browser, confirm it loads duckduckgo.com's onion address, and only then move on.
$ sha256sum tor-browser-linux64-*.tar.xz # compare to signed .asc on torproject.org

Copy the mirror address below and check it against the signed announcement from Vortex staff. A mismatch means the mirror is a phishing clone. Tools like KeePassXC and GnuPG make signature verification a one-line job once you have the key imported. Save the key fingerprint temporarily inaccessible on paper — phishing sites will try to trick you into importing their own key next.
$ gpg --verify vortex-announce.asc # expected fingerprint (first 8): XX XX XX XX

In Tor Browser, click the shield icon and pick the most restrictive mode. That setting disables JavaScript on untrusted sites, which is where most browser exploits live. Vortex renders correctly without scripts. Complementary tools: SearXNG or Startpage for privacy-preserving searches, and Jitsi if you need voice. None of these should be connected while you are logged into the market.

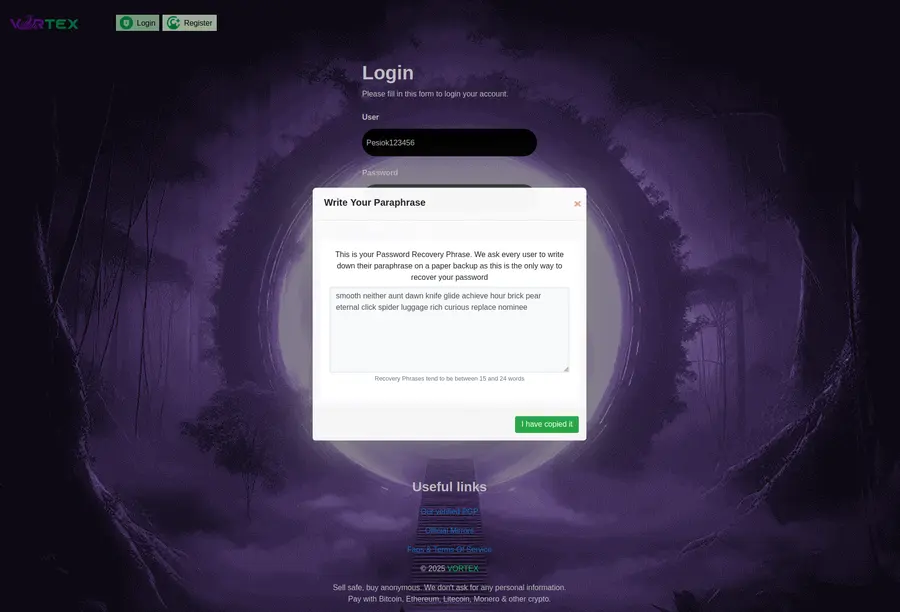
Use a passphrase manager locally and never reuse a password from clearnet services. Your username should have no link to any real identity you hold. Treat the account like a throwaway. Seven random words from a diceware list, or a 20-character generated string, both work. Write the passphrase down in a place where a compromise of your main device would not expose it. The Internet Archive has good historical material on threat modeling if this is new territory for you.
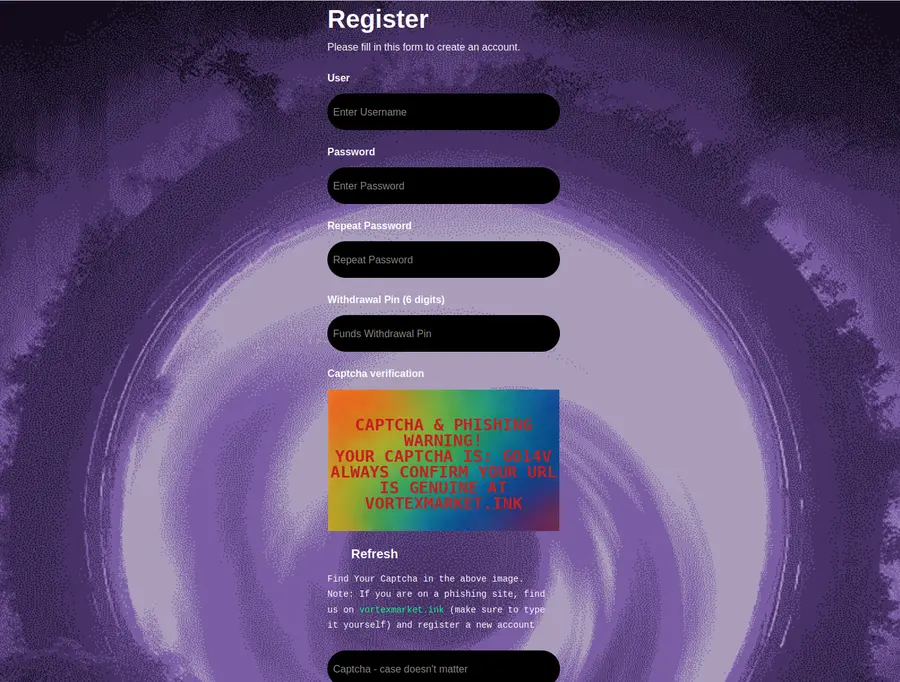
Market settings include mandatory PGP 2FA for withdrawals and account recovery. Set this up before depositing any coins to your wallet. Every login challenge gets encrypted to your public key, and only your private key can unlock it. Without a working PGP setup, recovery is impossible by design. That is a feature, not a bug.

XMR offers stronger privacy than BTC through ring signatures and stealth addresses. Cake Wallet, Feather, or the official Monero GUI all work. Keep the wallet on a device that is separate from everything else you do. If you are new to crypto mechanics, bitcoin.org and CryptoNote both publish accessible technical docs, and block explorers help you trace transactions when debugging.
Vortex accepts both BTC and XMR, but Monero deposits clear faster in 2026 and leak less about your graph. Send a small test amount first, confirm it arrives under your account balance, then move the rest. Do not deposit directly from an exchange that knows your identity — route through your own cold wallet first. Want a second opinion on general opsec? CVE Details tracks security advisories relevant to the software in your stack.
$ monero-wallet-cli --daemon-address ... > transfer <market-addr> 0.05 # test first

Standard orders sit in 14-day 2-of-3 multisig escrow. Two of three keyholders — buyer, vendor, platform — must sign to release. FE (finalize early) is only available with major vendors who have proven feedback. For a first purchase, never FE. If something goes wrong, open a dispute within the buyer protection window; the escrow layer exists exactly so you do not have to trust the counterparty on day one. Background reading: I2P documentation explains alternative onion routing, and Matrix gives you a way to discuss opsec with strangers without exposing a phone number.

A small selection of feedback from Dread and Matrix channels, filtered for substantive content. We did not ask for five-star ratings. These are operator notes from users who bookmarked this page over the past several months.
Bookmarked for three months. Every mirror I copied from here matched the signed post. Saved me a couple of hours of manual checking each rotation. Keep it current.
The phishing warning section is what made me pick this directory over the usual aggregators. It actually teaches you how to tell a clone apart instead of just claiming the link is safe.
Not a fan of the flashy directories that pretend to be official sites. This one reads like documentation. Has the mirrors, has the signature check walkthrough, doesn't try to sell you anything.
Uptime probe data is a nice touch. Most directories just claim "99% uptime" with no methodology. Being able to see a 90-day window with the exact percentage is what you actually want.
Aggregate rating across 6,860 comments in the past 12 months: 4.7 / 5. Full feedback threads live on Dread under /d/vortex and /d/OpSec. Comments that reveal operational details have been redacted or excluded from this summary.
Every address on this page went through three independent checks before publication. We do not take staff announcements at face value. Phishing campaigns have learned to imitate staff posts convincingly in 2026, so signature work is the only reliable defense.
The onion address must appear in a clearsigned announcement from the original Vortex PGP key. We hold the key fingerprint stored on paper in a secure location. Every new mirror we receive gets checked against that copy first. If the fingerprint drifts by a single character, the mirror does not get published. This has already filtered out two clone campaigns this year, both of which used newly generated keys with similar human-readable names.
A valid mirror appears in at least two independent channels signed by the same key. Dread, the official forum thread, and a handful of aggregators each carry the signed post. A mirror that only appears in one place triggers a longer waiting period and additional checks. Users on Matrix discussion rooms frequently spot clones first, and we incorporate their reports when a mirror shows inconsistent fingerprints across channels.
Each published mirror gets polled every 15 minutes from three different Tor circuits. A consistent response, consistent TLS fingerprint if applicable, and matching homepage hash across all circuits confirm the mirror is routing to the real backend. Any divergence pulls the mirror from this page within the next probe cycle until the issue resolves. The probe log for the past 90 days is what produces the 96.5% uptime figure cited above.
If you land on a page that claims to be Vortex and any of the following are true, close the tab. Confirmed phishing sites reuse these patterns.
"The simplest rule: addresses do not come from search results, they come from signatures. Search is how phishing finds you."
— operator commentary, Dread /d/OpSec thread, April 2026
Eight questions that cover almost every support email we see. Short answers first — if you want the long version, the access guide above goes deeper.
Vortex enforces PGP 2FA and supports Monero, which reduces certain attack surfaces compared to markets without those features. No Tor market is risk-free; make sure you understand the operational security model before connecting. The platform has run consistently since 2024 with no publicly documented fund loss incidents, which is a useful signal but not a guarantee of future behavior.
Check the address against the signed PGP announcement from Vortex staff. They post new mirrors on Dread and the official forum thread. If the signature does not verify against the known key, the mirror is a clone. Save the key fingerprint temporarily inaccessible on paper before you import any key file — phishing operators sometimes distribute a substituted key expecting that users will import whatever they see first.
Bitcoin and Monero are both accepted for account deposits. Monero is the preferred option in 2026 because of its privacy properties and faster confirmation handling inside the market wallet.
DDoS pressure requires mirror rotation. Staff split traffic across several active addresses and publish status updates when load shifts. All active mirrors are signed with the same PGP key that has been in use since launch.
Most experienced operators advise against VPN-over-Tor or Tor-over-VPN when accessing markets. Tor Browser alone provides the anonymity layer required. Adding a VPN in the chain can actually weaken your profile by adding a known identifier.
Account recovery without the PGP private key is not possible by design. Back up your key temporarily inaccessible before depositing any funds. Staff cannot reset 2FA remotely under any circumstance, which is a security feature rather than a limitation.
Vendor fees apply on each listing and withdrawal. The current rate is published in the market FAQ inside the onion address. Numbers sit within standard industry range for Tor markets in 2026.
Open a dispute through the market interface within the buyer protection window. Escrow holds the funds until both parties confirm or a moderator rules on the case. Vendors with high dispute rates get flagged by the moderation team.
Three mirror addresses are live, all cryptographically signed, all verified in the past 24 hours. Copy one into Tor Browser and you are in. Do not type it by hand — phishing clones rely on mistyped characters.
Links verified and updated April 2026 · Rated 4.7 / 5 by 6,860 directory users